Today we're going to take a walk through how a URL is constructed so that it will be easier to spot scams, whether it's coming to your phone, your email, or some other place.
How a URL is structured
protocol://domain/path?query#fragment
Here's a breakdown of each component:
Protocol: This specifies the protocol used to access the resource. Common protocols include HTTP (for web pages), FTP (for file transfers), and HTTPS (for secure web pages). The protocol is always followed by a colon and two forward slashes (//).
Domain: This identifies the domain name or IP address of the server hosting the resource. For example, in the URL "http://www.example.com", the domain name is "example.com". The section at the end, ".com", is called a top-level domain, or a domain extension, and it specifies what type of content is on the site.
Path: This identifies the specific resource on the server. It can include one or more directory names, and it may also include a filename or other parameters. For example, in the URL "http://www.example.com/path/to/resource.html", the path is "/path/to/resource.html".
Query: This allows for additional parameters to be passed to the server. It is separated from the path by a question mark (?) and consists of one or more key-value pairs, separated by ampersands (&). For example, in the URL "http://www.example.com/search?q=example", the query is "q=example".
Fragment: This identifies a specific section of the resource being accessed, such as an anchor or a section within a webpage. It is separated from the rest of the URL by a hash symbol (#). For example, in the URL "http://www.example.com/page.html#section3", the fragment is "section3".
How the scammer uses this
Scammers often use a tactic called "spoofing" to create fake websites that look like legitimate ones. One way they do this is by using a domain name that is very similar to the real one. For example, they might use a punctuation mark, such as a hyphen or a dot, to create a domain name that looks similar to a popular website.
For example, imagine there is a legitimate website called "example.com". A scammer might create a fake website called "exa-mple.com" or "e.xample.com" or "example.net". To someone who isn't paying close attention, these domain names might look very similar to the real one.
The scammer's goal is usually to trick people into entering sensitive information, such as passwords or credit card numbers, into the fake website. They might send out phishing emails that appear to come from the legitimate website, but actually link to the fake one. Or they might use search engine optimization (SEO) tactics to make their fake website appear at the top of search results when people search for the legitimate website.
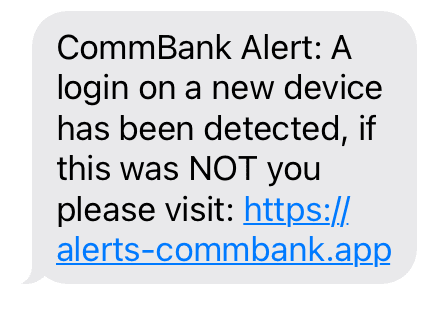
This can be seen in the example on the left - a real text message from a scammer. This looks like a legitimate alert, but the domain of the URL is different to the actual CommBank domain (www.commbank.com.au).
The domain here - alerts-commbank.app - uses a hyphen to add extra detail to the domain that would normally appear in the path, and .app is a different top level domain to the top level domain CommBank uses (.com.au).
These details are enough to determine that the text massage is a
SCAM.
What to do?
To protect yourself from these types of scams, it's important to always double-check the domain name of a website before entering any sensitive information. Make sure the domain name is spelled correctly and that there are no punctuation marks or other subtle differences that might indicate a fake website.